Sponsored by CyberGRX
Sponsored by LexisNexis Risk Solutions
True Cost of Fraud | APAC Study
Sponsored by NICE Actimize
Changing the Rules: The Evolution of Transaction Monitoring
Sponsored by Abnormal Security
Exploring the Rise of Israel-Based BEC Attacks
Sponsored by Palo Alto Networks
The Expert Guide to Mitigating Ransomware & Extortion Attacks
Sponsored by Feedzai
The Human Impact of Fraud and Financial Crime on Customer Trust in Banks
Sponsored by CyberGRX
The Ultimate Ransomware Survival Guide: How to Keep Your Business Safe
Sponsored by Mimecast
The State of Email Security 2023: Cyber Risk Has Entered The Boardroom
Sponsored by Proofpoint
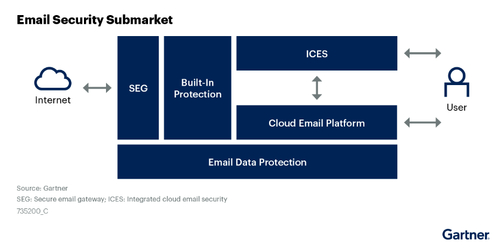
Proofpoint Recognized in Gartner® Market Guide for Email Security
Sponsored by Proofpoint
Breaking Down BEC
Sponsored by Expel
Cybersecurity 2023: The Trends and Predictions You Need to Know
Sponsored by Mimecast
$4.65 million | The Cost of Phishing Breaches
Sponsored by Mimecast
$265 Billion | Cost of Ransom Payments by 2031
Sponsored by Expel
Get the Most Out of Your (Growing) Security Tech Stack: Three Steps
Sponsored by Mimecast