Sponsored by Palo Alto Networks
Sponsored by Kayena
Pentesting Buyers Guide
Sponsored by Kaseya
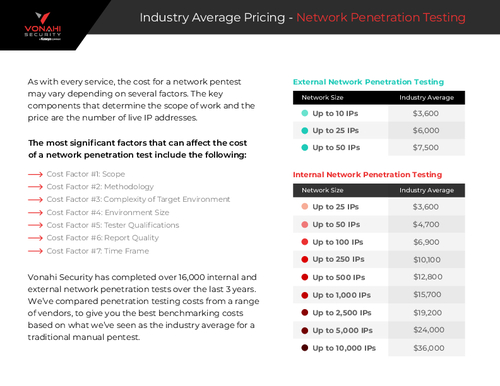
Industry Average Pricing - Pentesting
Sponsored by Kaseya
Top 10 Pentest Findings
Sponsored by ServiceNow
ITSM Spotlight: IT Infrastructure Library (ITIL4)
Sponsored by ServiceNow
3 Key Elements of IT Resource Management
Sponsored by CyberArk & Accenture
Securing Access for All Users: Why Every Identity, Including Digital Identities, Has Privileges
Sponsored by Palo Alto Networks
Whitepaper: Secure Access Service Edge (SASE)
Sponsored by Palo Alto Networks
5 Steps To Accelerate Your SASE Adoption and Improve Your Security Posture
Sponsored by Palo Alto Networks
NTT Managed Campus Networks with Palo Alto Networks Prisma SASE
Sponsored by Palo Alto Networks
5 Ways SASE Improves Your Security and Your Network
Sponsored by Palo Alto Networks
To Unlock Employee Productivity Securely, Make The Shift To SASE
Sponsored by Palo Alto Networks
Protect Your Digital Infrastructure with Managed SASE
Sponsored by ServiceNow
IT Modernization | Improving Service Delivery & Reduce Costs
Sponsored by Elastic