Sponsored by Proofpoint
Sponsored by Verisign
DDoS Attack Trends Report
Sponsored by Digital Guardian
The Definitive Guide to Data Loss Prevention
Sponsored by Digital Guardian
Meeting Stringent HIPAA Regulations: Your Guide To Safeguarding Patient Data
Sponsored by Digital Guardian
The Definitive Guide to Data Classification for Data Protection Success
Sponsored by Trend Micro
Evolving Threats Call for Integrated Endpoint Solutions with Holistic Visibility
Sponsored by Trend Micro
Securing the Server Compute Evolution: Hybrid Cloud Has Transformed the Datacenter
Sponsored by Trend Micro
There is No Silver Bullet: Why a Multi-layered Approach to Endpoint Security is a Must
Sponsored by Trend Micro
Beyond Next-gen: Defining Future-ready Endpoint Security
Sponsored by Trend Micro
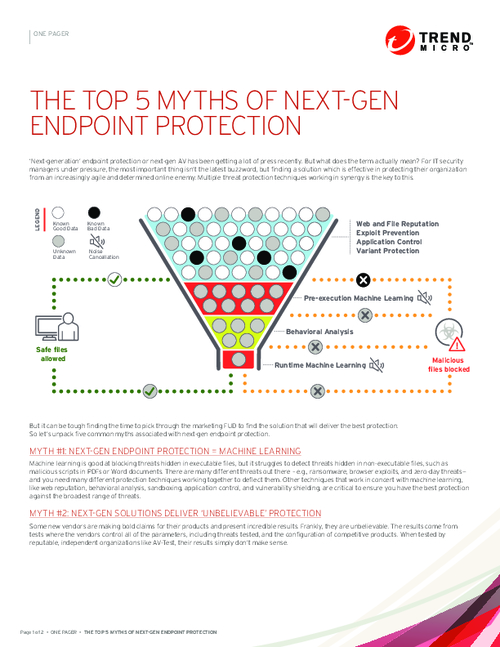
The Top 5 Myths of Next-Gen Endpoint Protection
Sponsored by Akamai
7 Critical Considerations for Choosing a Cloud Security Provider
Sponsored by BitSight
Rating the Security Performance of the Fortune 1000
Sponsored by Lastline
Ransomware: The Defender's Advantage
Sponsored by Symantec
Endpoint Security: Creating Order from Chaos
Sponsored by BioCatch